Guide to Windows PowerShell 4.0
Sunday, June 22nd, 2014Basic description and guidance for use:
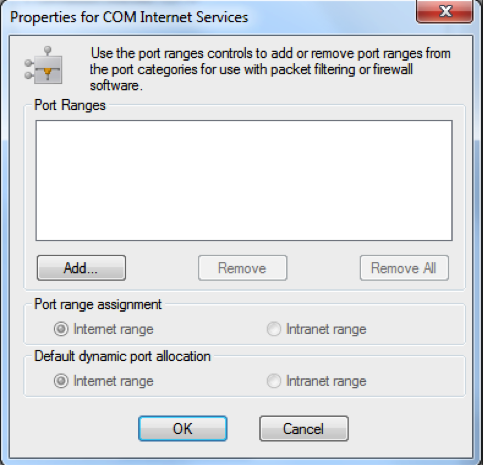
Windows PowerShell is a task automation and configuration management framework from Microsoft, consisting of a command-line shell and associated scripting language built on the .NET Framework. PowerShell provides full access to COM and WMI, enabling administrators to perform administrative tasks on both local and remote Windows systems as well as WS-Management and CIM enabling management of remote Linux systems and network devices.
In PowerShell, administrative tasks are generally performed by cmdlets, which are specialized .NET classes implementing a particular operation. Sets of cmdlets may be combined into scripts, executables, or by instantiating regular .NET classes. These work by accessing data in different data stores, like the file system or registry, which are made available to the PowerShell runtime via Windows PowerShell providers.
Microsoft Windows PowerShell 4.0 is the version of the PowerShell scripting language found in Windows Server 2012 R2. Windows PowerShell 4.0 is backward compatible. This means that cmdlets, providers, modules, snap-ins, scripts, functions, and profiles that were designed for Windows PowerShell 3.0 and Windows PowerShell 2.0 work in Windows PowerShell 4.0 without changes. Some of the new features in Windows PowerShell 4.0 include:
o Support for workflow and remote script debugging
o Improved workflow authoring experience to make it more consistent with script authoring
o Added PipelineVariable as a common parameter
o Better support for downloading updatable help by using Save-Help and Update-Help in offline scenarios
o Updated version from 3.0 to 4.0
o Several bug fixes and performance improvements
Windows PowerShell Integrated Scripting Environment. Windows PowerShell ISE in Windows Management Framework 4.0 introduces:
o Support for Windows PowerShell Workflow debugging
o Support for remote script debugging
o IntelliSense support for Windows PowerShell Desired State Configuration resources and configurations
PowerShell 4.0 comes preinstalled for Windows 8.1 and Windows Server 2012 R2, but there are those who still prefer Windows 7 and other earlier server operating systems. So, it’s great to see that Microsoft has finally released PowerShell 4.0 as part of the Windows Management Framework (WMF) 4.0 release. The release supports Windows 7, Windows Embedded Standard 7, Windows Server 2008 R2, and Windows Server 2012.
Windows PowerShell 4.0 is part of the Windows Management Framework 4.0, which includes the following:
o Windows PowerShell
o Windows PowerShell ISE
o Windows PowerShell Web Services
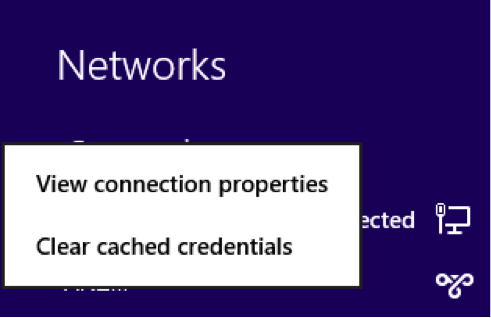
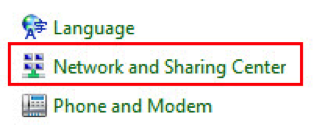
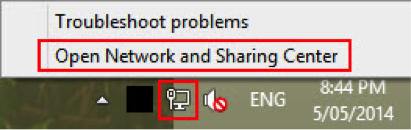
o Windows Remote Management
o Windows Management Instrumentation
o Server Manager WMI provider
o Windows PowerShell Desired State Configuration
Windows Management Framework 4.0 supportability matrix
|
Operating system |
Windows PowerShell 4.0 available |
Prerequisites |
Installation file |
| Windows Server 2012 R2 | Built-in | N/A | N/A |
| Windows 8.1 | Built-in | N/A | N/A |
| Windows Server 2012 | Yes, part of WMF 4.0 | .NET 4.5 (built-in) | x64: Windows8-RT-KB2799888-x64.msu |
| Windows 8 | No, user must upgrade to Windows 8.1 | N/A | N/A |
| Windows Server 2008 R2 | Yes, part of WMF 4.0 | Windows Server 2008 R2 SP1, .NET 4.5 | x64: Windows6.1-KB2819745-x64-MultiPkg.msu |
| Windows 7 | Yes, part of WMF 4.0 | Windows 7 SP1, .NET 4.5 | x64: Windows6.1-KB2819745-x64-MultiPkg.msu, x86: Windows6.1-KB2819745-x86.msu |
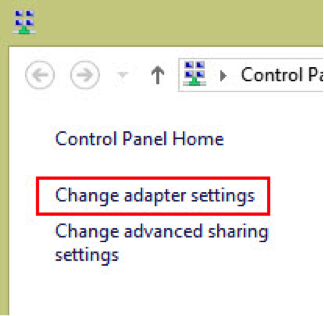
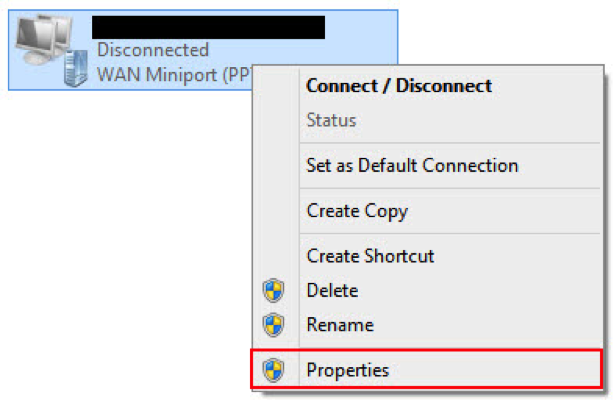
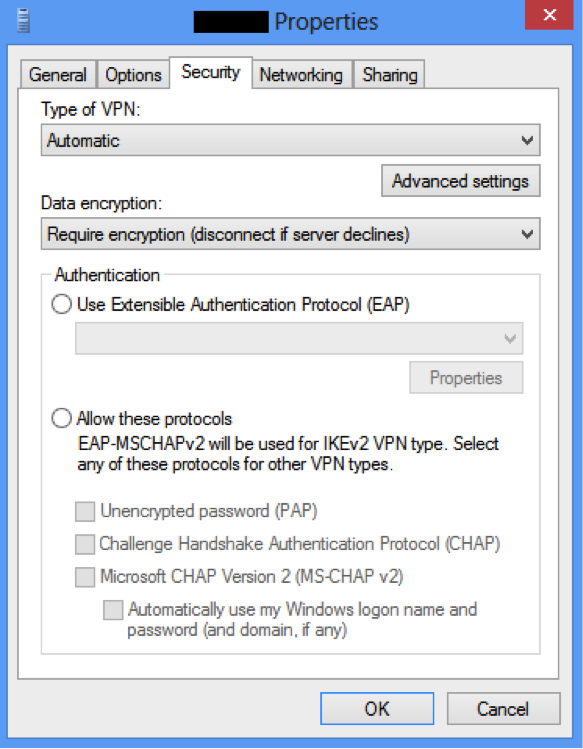
Installation:
o Verify that all prerequisites are installed according to the Windows Management Framework 4.0 supportability matrix above.
o Run the installation file applicable to the operating system
o Reboot the computer, start Windows PowerShell and verify that the output of $PSVersionTable shows 4.0 as the value of the PSVersion property