Elliptic Curve Cryptography (ECC)
May 21st, 2014 by Rossy GuideWhat is this?
Elliptic Curve Cryptography (ECC) comes to public key cryptography based on elliptic curve theory that can be used to create faster, smaller, and more efficient cryptographic keys. Elliptic curves are also used in several integer factorization algorithms and ECC generates keys through the properties of the elliptic curve equation instead of the traditional method of generation as the product of very large prime numbers. The technology can be used in conjunction with the other popular algorithms such as RSA, and Diffie-Hellman.
ECC has a reputation of being quite complex and it has been integrated into popular open-source cryptographic software including OpenSSH and OpenSSL, and it’s not inherently any more difficult to use than RSA.
History:
ECC was discovered in 1985 by Victor Miller (IBM) and Neil Koblitz (University of Washington). Also, It was developed by Certicom, a mobile e-business security provider, and was recently licensed by Hifn, a manufacturer of integrated circuitry (IC) and network security products. RSA has been developing its own version of ECC. And many manufacturers, including 3COM, Cylink, Motorola, Pitney Bowes, Siemens, TRW, and VeriFone have included support for ECC in their products.
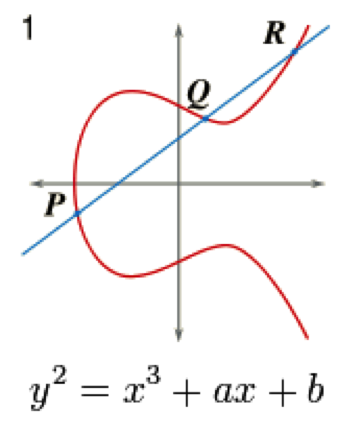
The equation of an elliptic curve is given as,
The following few terms that will be used,
E: Elliptic Curve
P: Point on the curve
n: Maximum limit (prime number)
Simple elliptic curve
Key Generation
It is an important part where we have to generate both public key and private key. In this, the sender will be encrypting the message with receiver’s public key and the receiver will decrypt its private key.
Now, we have to select a number ‘d’ within the range of ‘n’.
To generate the public key, using the following equation
Q = d * P
For above, d = the random number that we have selected within the range of (1 to n-1). P is the point on the curve. And ‘Q’ is the public key and the ‘d’ is the private key.
Encryption
Let ‘m’ be the message that we are sending. In this, we have to represent this message on the curve. These have in-depth implementation details. All the advance research on ECC is done by a company called certicom.
Consider ‘m’ has the point ‘M’ on the curve ‘E’. Randomly select ‘k’ from [1 – (n-1)].
Two cipher texts will be generated let them be C1 and C2.
C1 = k*P
C2 = M + k*Q
For the above, C1 and C2 will be send.
Decryption
We have to get back the message ‘m’ that was send to us,
M = C2 – d * C1
For the above, M is the original message that we have send.
Features:
ECC is an approach to public-key cryptography based on the algebraic structure of elliptic curves over finite fields. And Elliptic curve variants of cryptographic algorithms have the following practical features.
o They are small and fast.
o Creating a new curve is uneasy.
o Elliptic curves can be used to factor integers.
o Some elliptic curves allow for pairings.